Documentation Index
Fetch the complete documentation index at: https://support.entegrata.com/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Firewall rules control which external services and resources your Entegrata instance can communicate with. Rules are organized by data source — making it easy to see exactly which policies apply to each integration — and by system-level rules for infrastructure-wide access. This is a critical security feature that:- Restricts outbound connections to only approved destinations
- Prevents unauthorized data exfiltration
- Ensures compliance with security policies
- Enables safe communication with data sources and third-party services
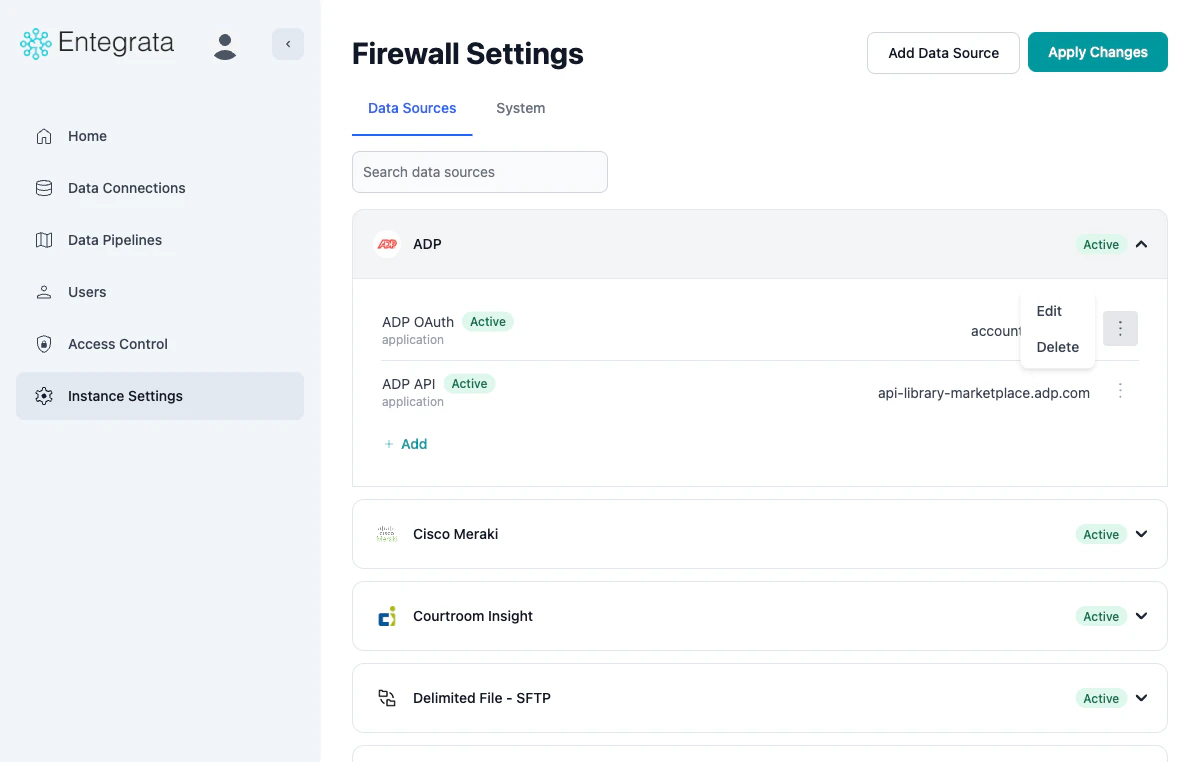
Navigating Firewall Settings
To access firewall settings, navigate to Instance Settings and click Manage Firewall Rules on the Firewall Settings card. The card displays a summary of your current application and network rule counts.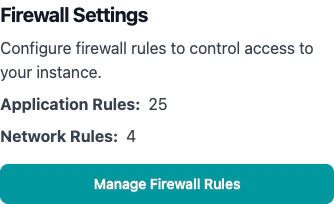
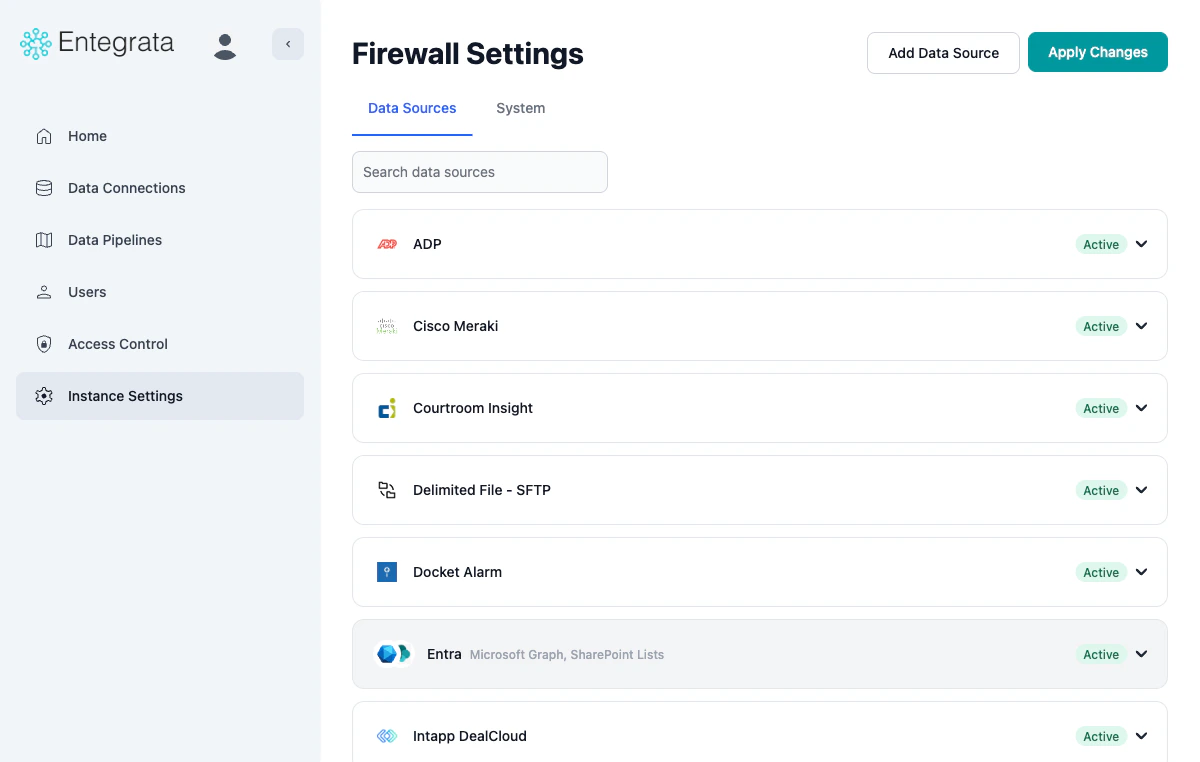
- Data Sources
- System
- Data source icon and name — identifies the integration
- Status badge — Active (at least one policy configured) or Inactive (no policies yet)
- Expand/collapse arrow — click to view individual policies
Understanding Firewall Policies
Policy Types
Each firewall policy is one of two types:- Application Policies (FQDN)
- Network Policies (IP/CIDR)
- Cloud APIs (e.g.,
api.example.com) - SaaS platforms (e.g.,
app.salesforce.com) - Services with dynamic IPs
- Exact domains:
api.example.com - Wildcard subdomains:
*.example.com
Policy Display
When you expand a data source or view the System tab, each policy row shows: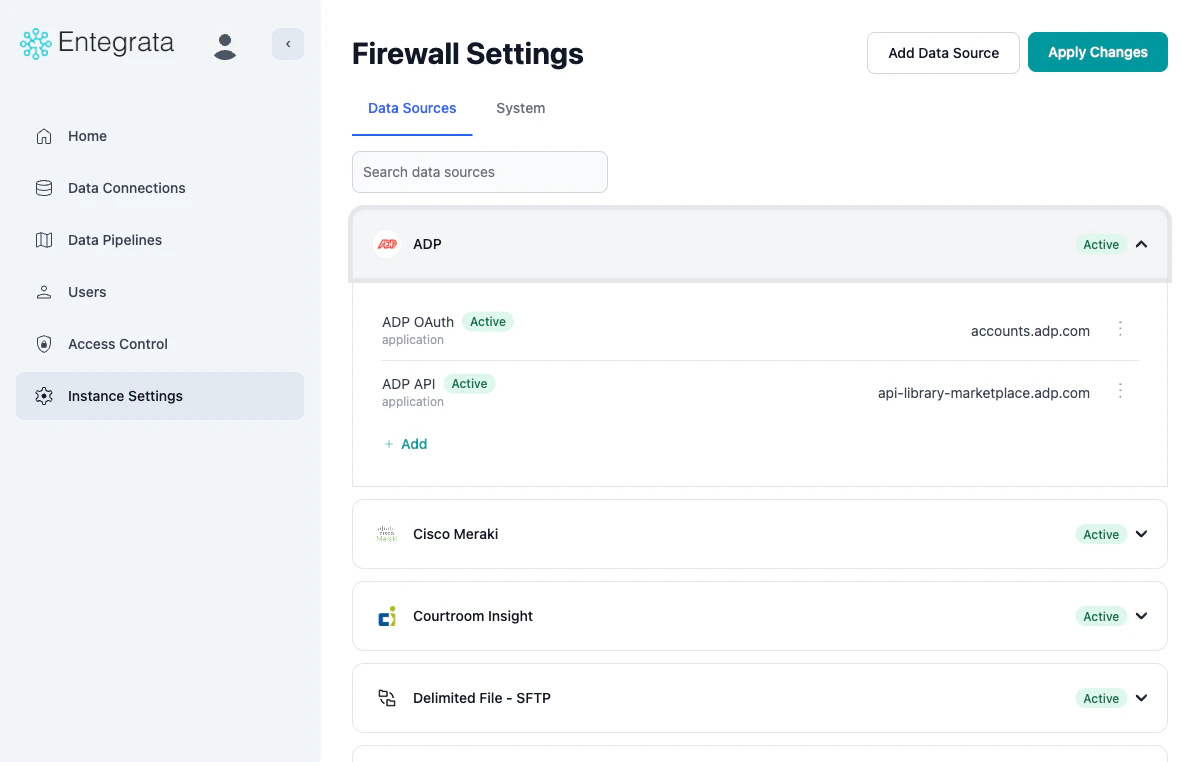
- Pending — The policy has been saved but not yet deployed. It will become active after you click Apply Changes and the infrastructure transition completes.
- Active — The policy is deployed and enforced on your infrastructure.
accounts.adp.com, 1.2.3.4/32).Adding a Data Source
Use this workflow to add firewall policies for a new data source integration.Open the Add Data Source Dialog
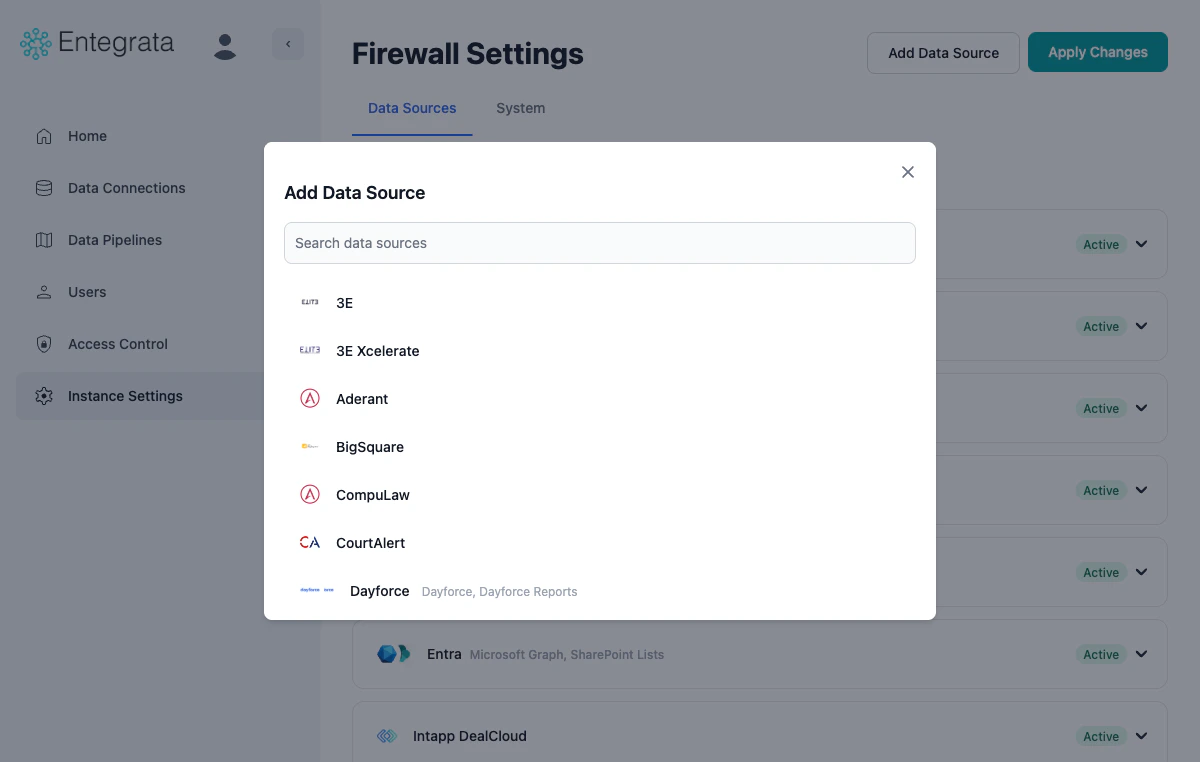
Select a Data Source
Add Policies
- Enter the IP address/CIDR range or domain in the text field
- Click Add to save the policy
- Click Done when finished
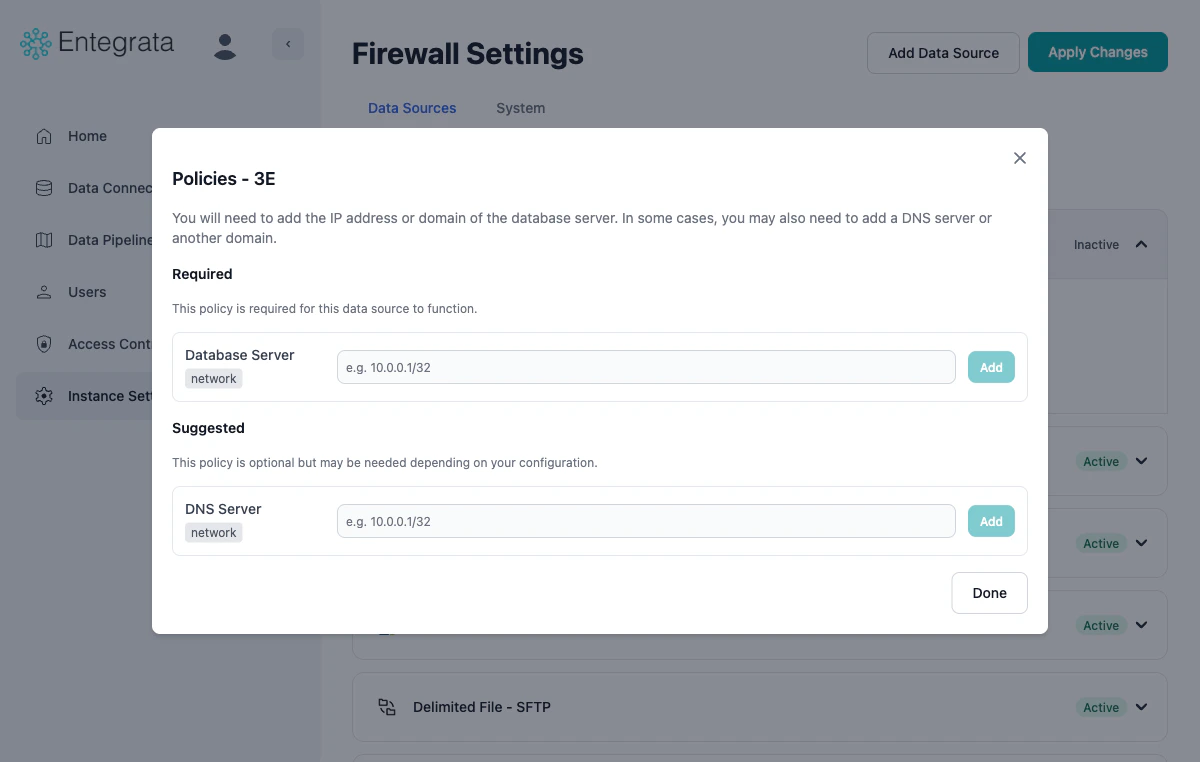
e.g. 10.0.0.1/32).Review Pending Policies
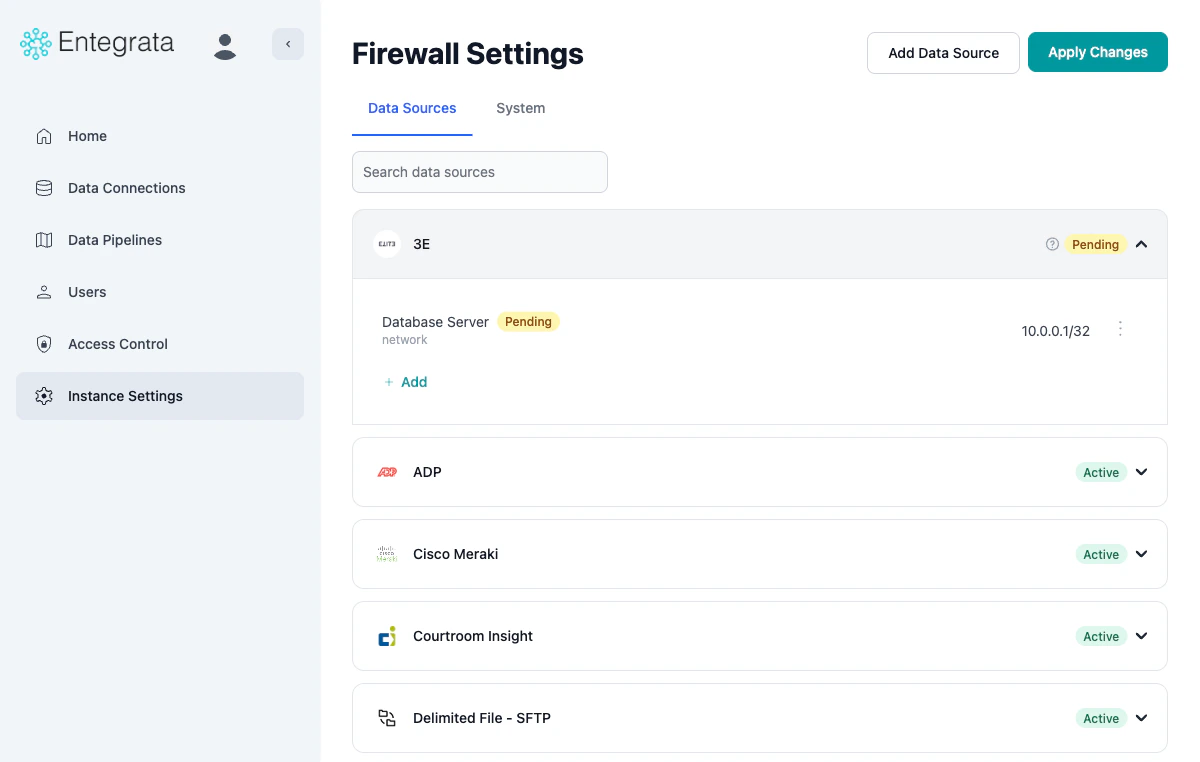
Removing a Data Source
If a newly added data source is not needed, click Remove in the expanded data source card to remove it before applying changes.Adding a System Policy
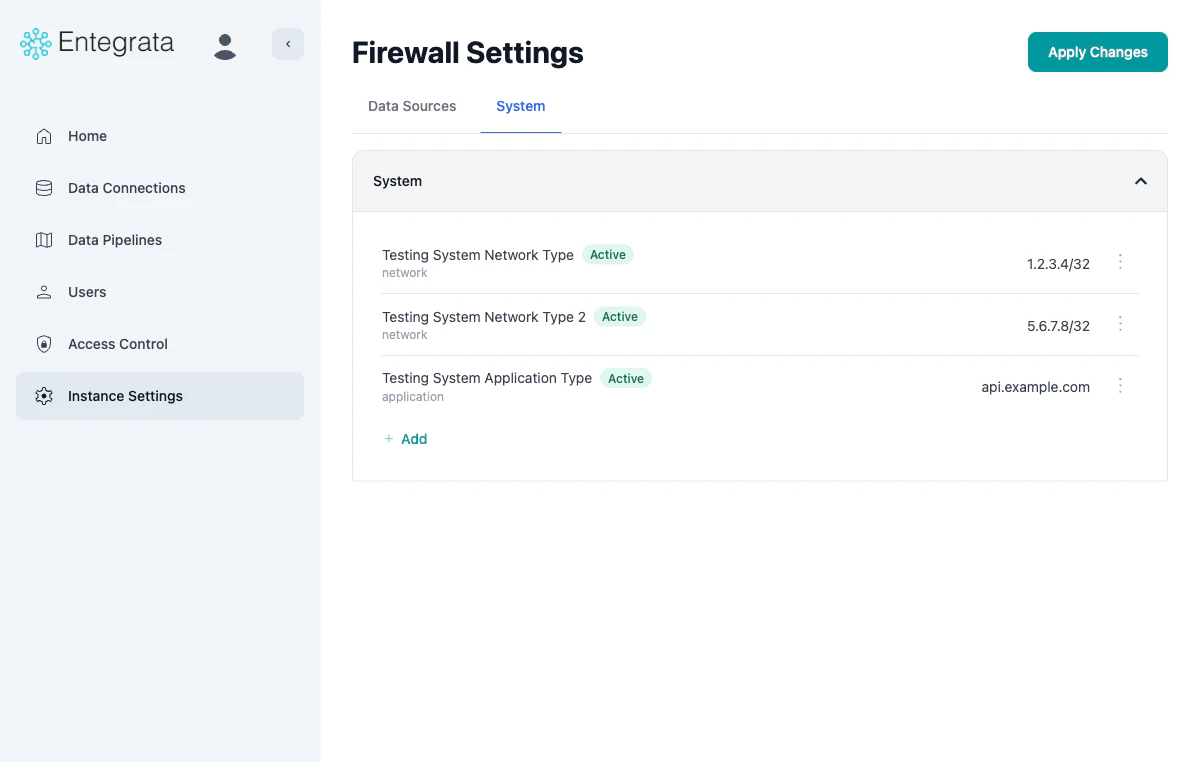
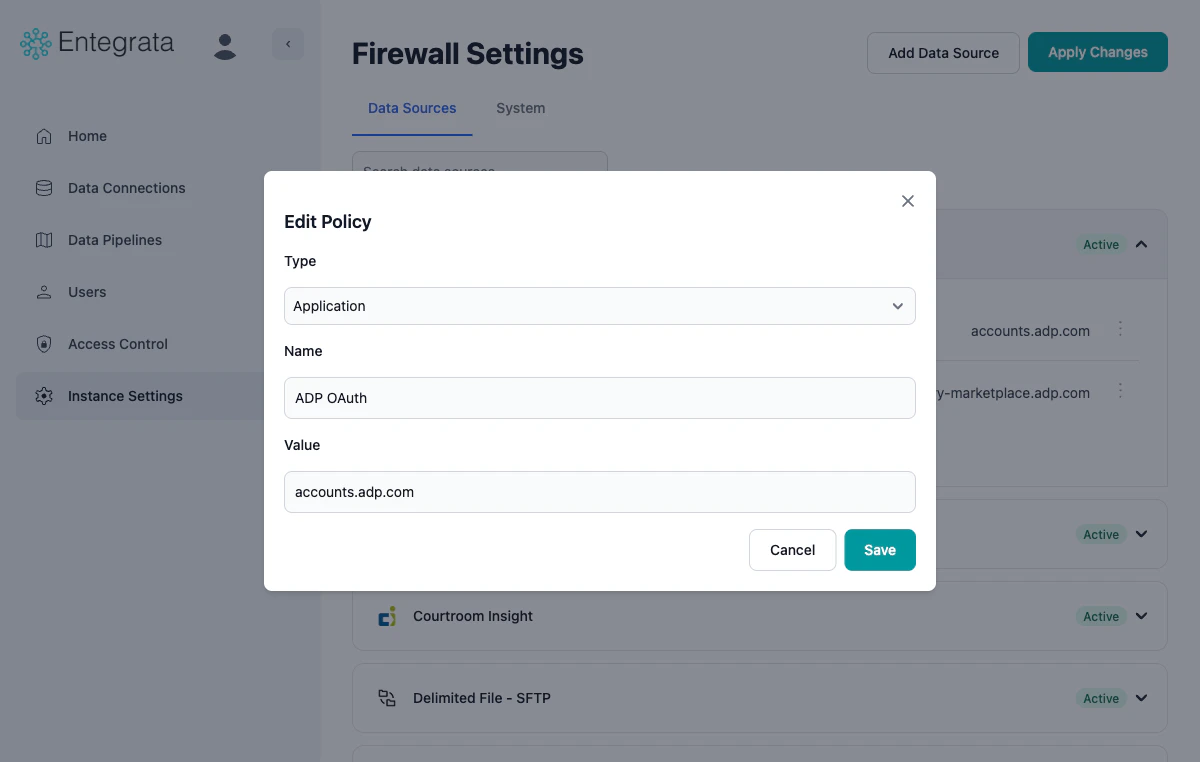
Use this workflow to add custom system-level firewall policies.Configure the Policy
- Type: Select Network (for IP/CIDR) or Application (for FQDN)
- Name: Enter a descriptive policy name
- Value: Enter the IP address/CIDR range or domain name
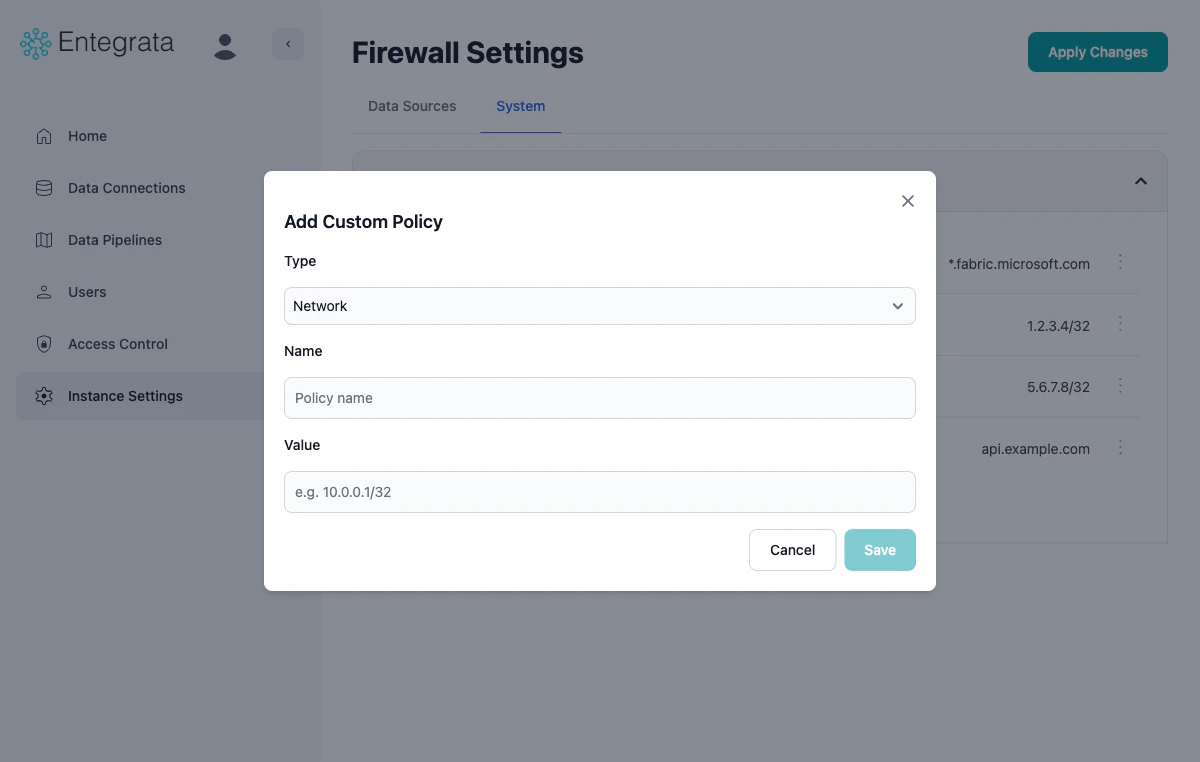
e.g. 10.0.0.1/32 for Network or a domain format for Application.Save the Policy
Adding a Policy to an Existing Data Source
You can add additional policies to data sources that are already configured.Expand the Data Source
Configure and Save
Editing a Policy
Locate the Policy
Open the Edit Dialog
Update the Policy
Deleting a Policy
Applying Firewall Changes
Understanding the Save-Then-Apply Workflow
Firewall management uses a save-then-apply workflow. When you add or edit a policy, it is saved with a Pending status. Pending policies are not enforced on your infrastructure until you click Apply Changes and the transition completes, at which point they become Active.Wait for Transition
- Status changes to Transitioning
- A loading screen displays progress
- The system polls for completion every 30 seconds
- Changes are deployed via Pulumi Infrastructure as Code
Why Save-Then-Apply?
During Transition State
While your instance is in Transitioning state:- Existing firewall policies remain active
- Data collection continues normally
- You cannot make additional firewall changes
- You cannot modify other instance settings
- You cannot apply new changes until transition completes
Validation Rules
Valid FQDN Examples
Valid FQDN Examples
api.salesforce.com*.azure.comapp.subdomain.example.comservice-123.cloud.provider.netmy-api.example.co.uk
Invalid FQDN Examples
Invalid FQDN Examples
*.com(wildcard too broad)example(missing TLD)http://api.example.com(includes protocol)api.example.com:443(includes port)api..example.com(double dots)
Valid IP/CIDR Examples
Valid IP/CIDR Examples
192.168.1.100192.168.1.100/3210.0.0.0/24172.16.0.0/16203.0.113.0/28
Invalid IP/CIDR Examples
Invalid IP/CIDR Examples
256.1.1.1(octet > 255)192.168.1.1/33(CIDR > 32)192.168.1(incomplete IP)2001:db8::1(IPv6 not supported)192.168.1.1-192.168.1.10(range notation not supported)
Troubleshooting
Collector fails after adding firewall policy
Collector fails after adding firewall policy
- Check if the policy status is still Pending — policies are not enforced until they reach Active status after applying changes
- Wait for any Transitioning state to complete
- Double-check the policy value matches the collector’s actual endpoint
- Ensure the policy uses the correct type (application for domains, network for IPs)
- Check collector logs for the actual connection target
Data source shows Inactive after adding policies
Data source shows Inactive after adding policies
- Ensure at least one Required policy has been added
- Verify the policy value passed validation (no error messages in the form)
- Try removing and re-adding the data source
Cannot find a data source in the Add Data Source dialog
Cannot find a data source in the Add Data Source dialog
- Check the search field for typos
- The data source may already be added — check the Data Sources tab
- If the data source is not in the catalog, add rules manually via the System tab
Wildcard policy doesn't work as expected
Wildcard policy doesn't work as expected
*.example.commatchesapi.example.combut NOTapi.sub.example.com- For nested subdomains, add multiple rules or use exact domains
*.example.comdoes not matchexample.comitself — add both if needed- Verify the policy has been applied (not just saved)
Changes stuck in Transitioning state
Changes stuck in Transitioning state
- Wait at least 15-20 minutes for infrastructure updates
- Refresh the page to see current status
- Check Azure portal for alerts in your subscription
- If it persists beyond 30 minutes, contact Entegrata support
Security Best Practices
Firewall Security Recommendations
- Only allow access to services actively in use
- Use specific FQDNs over wildcards when possible
- Prefer /32 CIDR (single IP) over broad ranges
- Use the guided policy setup when adding data sources — it recommends only what’s needed
- Review firewall policies quarterly
- Remove data sources that are no longer in use
- Verify policies match active collectors and integrations
- Use the search feature to quickly audit specific data sources
- Test policy changes in non-production environments first
- Batch related changes and apply them together
- Coordinate firewall changes with your security team
- Plan changes during maintenance windows